CC2.3 in plain language
SOC 2 includes a bucket of criteria about talking to people outside your building. CC2.3 is the one that asks whether you have a credible story for how customers, partners, or other outsiders find out when your service is unhealthy—and how you handle inbound noise when they report trouble. Nobody prescribes Slack vs. email vs. a dashboard; what matters is whether your practice is real, owned, and inspectable.
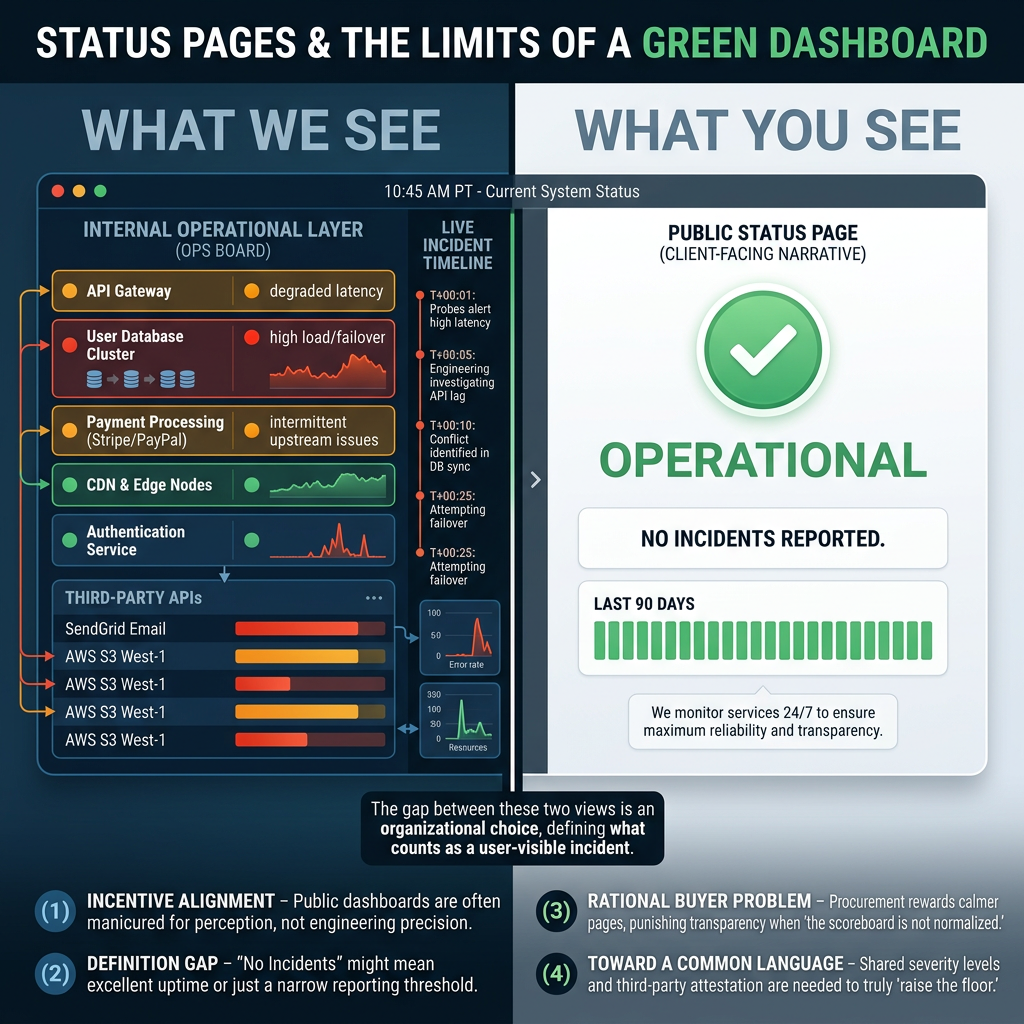
From an engineering standpoint, that usually means your operational truth (what broke, when you knew, what you did) should not diverge from your customer-visible narrative (what you published or escalated). Status boards and incident records are two sides of the same coin: one faces users, one faces the team, and both should line up under scrutiny.
What tends to get scrutinized
Examiners are not scoring your prose. They are looking for whether communication is early enough to be useful, sequenced enough to reconstruct causality, and boring enough to repeat every quarter. In practice that often surfaces as questions about: whether users discover outages only through support tickets; whether leadership can replay an hour-by-hour story; whether on-call and customer messaging point at the same facts; and whether post-incident write-ups reference artifacts that actually existed at the time.
Exemplar SRE as one layer of that story
We built Exemplar SRE so reliability work—health views, incidents, maintenance, and vendor-side context—lives in one place instead of scattered exports. That is useful on its own; it also makes it harder for "what we told customers" and "what we did internally" to drift apart under review.
Status boards
Dashboards you configure, plus history, give you a defensible picture of how availability and dependencies moved during an event—handy when someone asks what the system looked like at 2:14 a.m., not only what Slack said at 2:20.
Incidents
Workflows, ownership, and timelines give you an internal spine you can align with external updates: declare, route, mitigate, close, learn—without inventing a second paper trail after the fact.
Maintenance
Scheduled change and downtime, captured where you operate, reads as forethought: you planned the work, told people in advance, and did not treat surprise as the default communication mode.
Alerts and vendor feeds
When your own probes and third-party status sit beside each other, fewer incidents start with "we had no idea the provider was red." Fewer surprises usually means fewer mismatched messages to customers.
A word of care
Software cannot sign your attestation report. Tools only make it easier to behave consistently and to show your work. For anything binding, lean on counsel and whoever owns your control framework—then wire the product so day-two operations match what you claimed.
General commentary only—not legal, audit, or attestation advice.